Secure Workflow Automation with FTAPI SecuFlows.
Securely digitize and automate sensitive data workflows.

Secure data workflows for smooth work.
FTAPI SecuFlows
Say goodbye to repetitive and error-prone workflows. Automate your business processes in which data is recorded, exchanged or further processed: FTAPI offers you a cross-system solution for the secure digitization and automation of recurring data workflows.
Meet all legal requirements for the secure transfer of sensitive data and automate your digital workflows. FTAPI’s encrypted data workflow automation ensures the highest level of data security. The audit-proof workflow automations allow subsequent data manipulation.
Collect, exchange and process data. With FTAPI SecuFlows.
Secure data workflows for smooth work.
Functions.
- Simple integration into the existing system landscape
- Modular structure & numerous interfaces
- Highly scalable data workflow solutions
- Possibility of end-to-end encryption
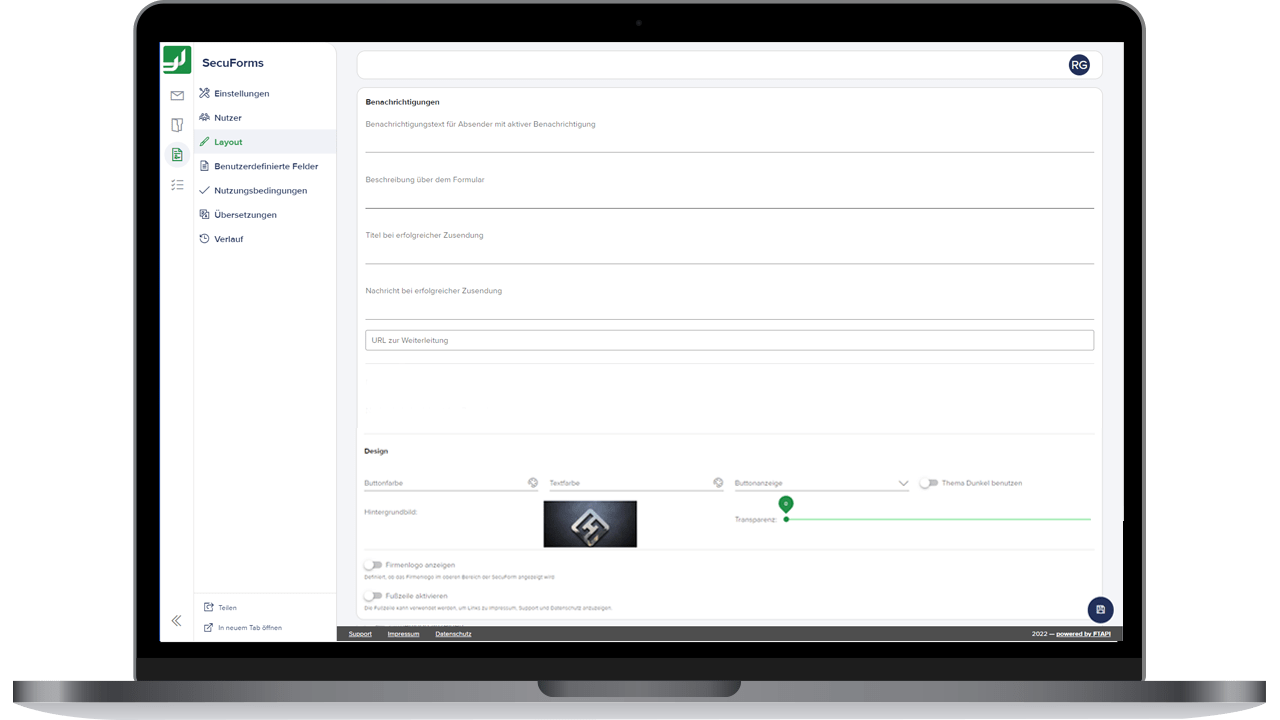
- Easiest configuration (low-code solution)
Areas of application.
- Automatic document dispatch
- Automatic processing of data input
- Automatic data synchronization
- Automatic generation of shares
- Automatic archiving
Your advantages with FTAPI SecuFlows.
Highest security
Increase in efficiency
FTAPI SecuFlows optimize workflows and reduce the workload of repetitive tasks.
Digitize flexibly
High quality standard
More time for important things
Rapid rollout and ROI
Part of the holistic FTAPI Secure Data Workflow platform.
The FTAPI SecuFlows are part of the comprehensive FTAPI platform with leading, established and flexible encryption technology for guaranteed legally compliant security in data workflows.
It guarantees very high compatibility and uniformity of the products and enables the simple and secure implementation of even more complex challenges in manual and automated data transfer – everything from a single source.
Over 2000 companies and more than 1 million active users trust in secure data and file transfer with FTAPI.
Sales & Account Management,
Head of DSAG Human Resources Switzerland

Benefits for your company.
The potential of digitization lies in the complete automation of digital workflows in order to relieve employees and optimize work processes in the long term. FTAPI offers you reliable and efficient automation of data workflows.
Due to the highest protection of your data, workflows can be mapped GDPR-compliant. With FTAPI SecuFlows you not only optimize data security, you also reduce the error rate of your business processes and increase productivity.
Optimize processes.
- More efficient workflows
- Improved customer experience
- Workflow scalability
- Meet compliance requirements
- GDPR compliant encryption
Identify your automation potential with the FTAPI experts.
Benefits for your administrators.
A digital process is not automatically an efficient process: system barriers arise again and again as a result of digitalization. This is exactly where FTAPI comes in and combines the technologies and solutions you use for data transfer into an integrative overall system.
Data and documents can thus be exchanged securely, quickly and fully automatically between people, machines and systems. Let your data flow – but securely: With FTAPI SecuFlows you guarantee a highly secure automated workflow.
Let data flow safely.
- Fast rollout and low support requirements
- No-Code/Low-Code implementation
- Harmonization of your system landscape
- Highest data protection and compliance
- Easy connection of your systems via common interfaces
Benefits for your employees.
You share more and more data and documents with different partners, customers or colleagues. In many places, data exchange is still manual or partially automated. This procedure entails a high susceptibility to errors and monotony.
FTAPI simplifies digital workflows and automates repetitive work processes – simple, secure and completely uncomplicated. The possible applications are cross-departmental and practically unlimited.
Goodbye monotonous. Hello workflows.

- Relief in everyday work
- Fast completion of repetitive tasks
- More time for demanding tasks
- Greater satisfaction and motivation
- Error prevention
Frequently asked questions about automated data workflows.
Any workflow or business process that requires interactions with people and/or between systems and is routine and recurring is predestined for automation.
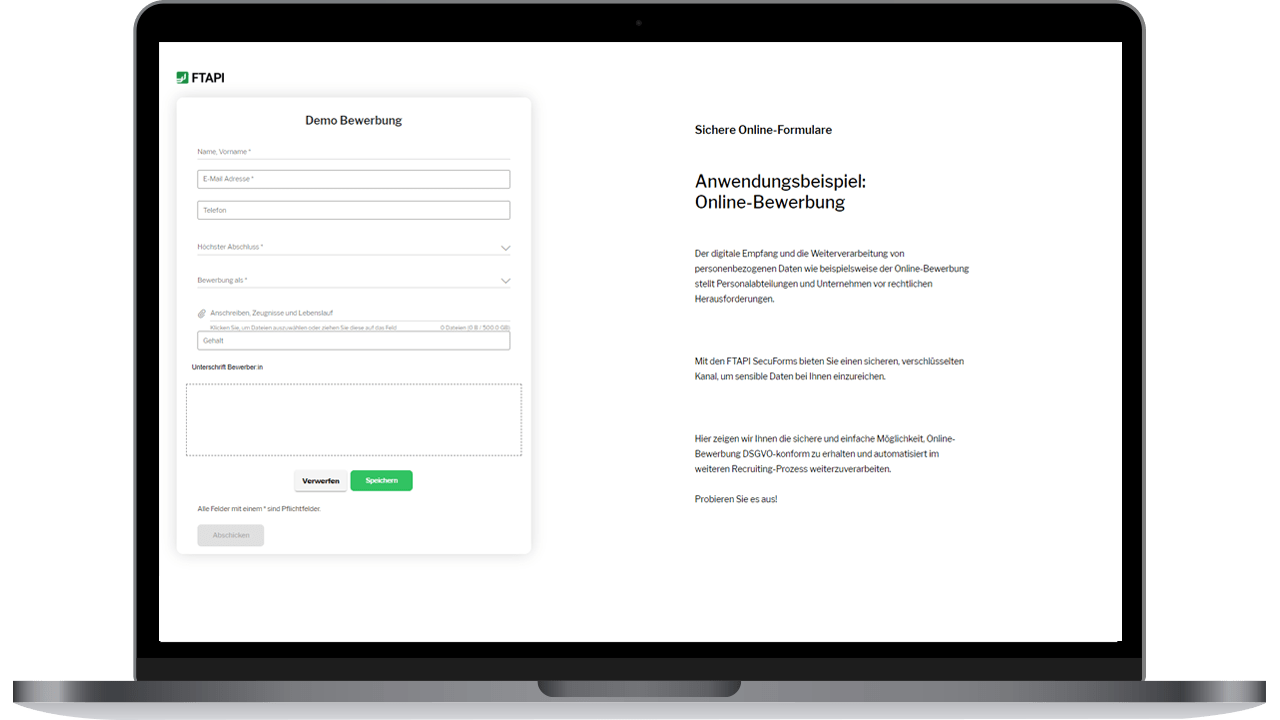
There are almost no limits to the imagination here: In principle, all digital data can be made usable and processed using an automated workflow, provided they are accessible in the source systems via an interface. Interfaces such as file systems, Rest-API, FTP but also FTAPI products such as SecuForms, SecuTransfer or SecuRooms can be used.
Our Technical Implementation Team works with you to identify the workflows that you can automate effectively and scalably.
Examples of automated workflows
- Automated customer / citizen communication
- Automated payroll
- Automated master data update
- Automated application submission
- Automated data synchronization
- Automated (corona) report query
- Automated credit check
- Automated transmission of test results and scan data
- and many more…
And what not to automate:
- Direct interaction with people
- Decisions that affect people and require emotional understanding
- Non-Recurring Themes
- Topics that need creative solutions.
f you already have a specific procedure or business process in mind that should be automated, we will discuss the technical requirements and the implementation process with you.
If you don’t have a use case in mind yet, we would be happy to identify individual workflows for your company together with you in a workshop. We develop concrete approaches based on your system landscape, internal structures and technical indicators.
We offer an increasing number of business processes in a quasi-standardised manner. This means that only a short check of your specific requirements (third-party systems, interfaces, type and provision of the data) is necessary and our team can then immediately start implementation. Such automated workflows can usually be deployed within a few days.
Our promise: On average, implementation only takes a few hours or a few days. Your data is safe and will be treated confidentially. No lengthy projects and no code are necessary.
The client for automation runs locally at the customer. It is installed as a service under Windows or Linux. The hardware requirements depend on the business process that is to be automated. As a rule, servers with 4 cores and 8-12 GB RAM are sufficiently equipped.
If you are interested in implementing a SecuFlow, our Technical Implementation Team will discuss the specific requirements with you and carry out a brief system check.